Welcome to DeFi Due Diligence
You know that feeling when you wake up to 30 text messages asking you to verify a login you never attempted?
That's not paranoia. That's the new normal after the biggest credential leak of 2026 just dropped.
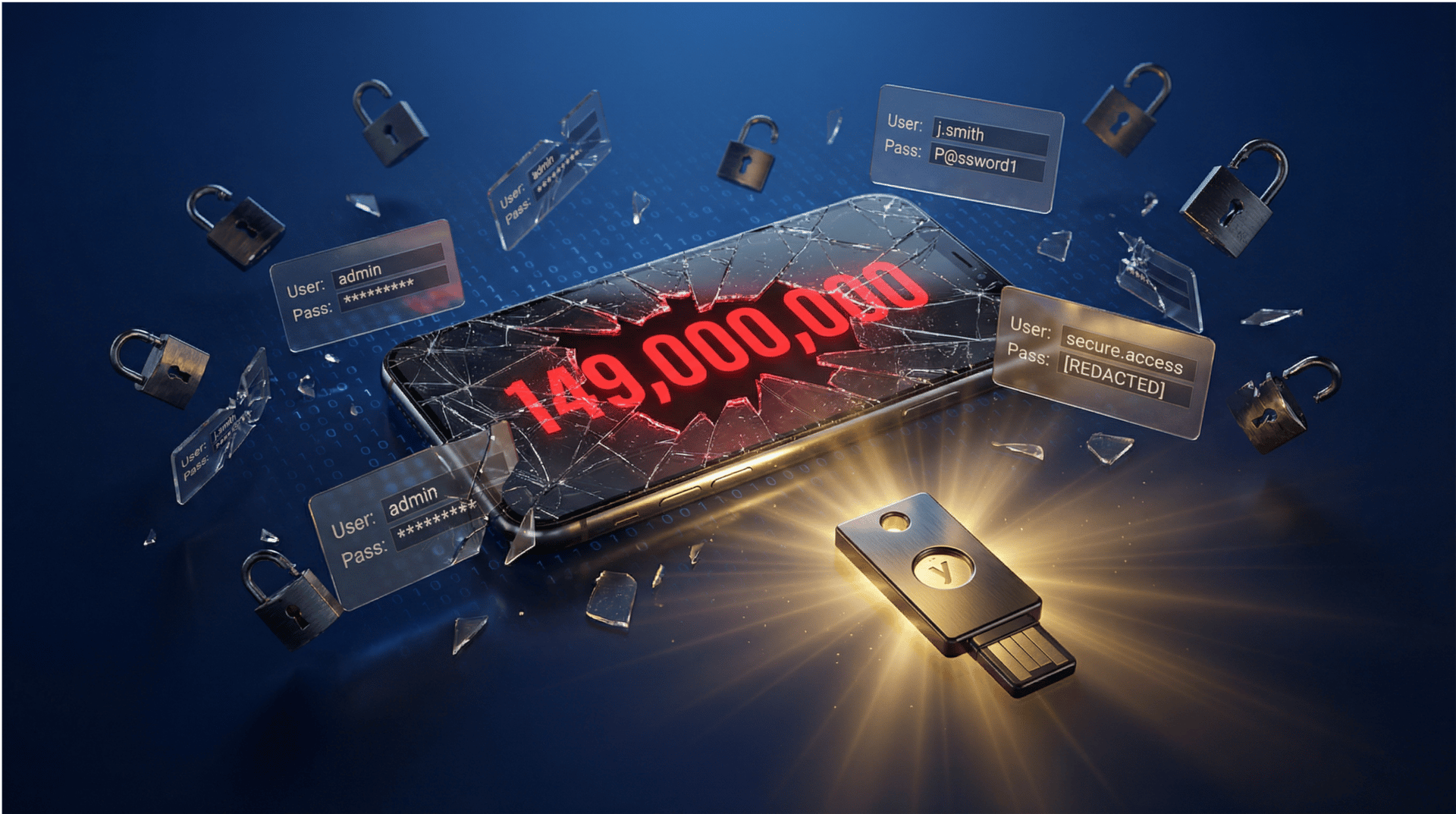
149 million login credentials. No encryption. No password protection. Just sitting there on a publicly accessible database.
And 420,000 of them were Binance accounts.
If you use the same password across multiple sites, or if you're still using SMS for 2FA, this one's going to hurt.

The Leak That Made SMS 2FA Useless
Here's what happened:
A database containing 149 million login credentials was discovered this week. Not hashed. Not encrypted. Just plain text emails, usernames, passwords, and account login URLs.
420,000 of those credentials were for Binance accounts. The rest? Instagram, Facebook, Roblox, and dozens of other platforms.
To be clear: this wasn't a Binance breach. These credentials were harvested by infostealer malware from users' infected devices over time, then compiled into this database. Binance's systems weren't compromised - but if your device was ever infected, your login is now public.
Oh, and the database itself contained malware designed to steal even more credentials from anyone who accessed it.
The result: Binance users are now reporting 30+ 2FA requests per day. Attackers are hammering login attempts around the clock, hoping someone slips up and approves one.
Worse, phishing SMS messages are now circulating claiming to be from Binance, asking users to "confirm Trezor registration" or "verify withdrawal address." Click the link, enter your credentials, and your account is gone.
Why SMS 2FA won't save you:
SMS can be intercepted through SIM swaps or SS7 attacks. If an attacker has your password and your phone number (both in this leak), they can social engineer your carrier or exploit telecom vulnerabilities to intercept your 2FA codes.
You think you're protected. You're not.
What's actually in the leak:
Data Type | Included? |
|---|---|
Email addresses | Yes |
Usernames | Yes |
Passwords | Yes |
Account login URLs | Yes |
Phone numbers | Unknown (likely) |
2FA backup codes | No (yet) |
The scary part? This database was publicly accessible. Anyone could download it. Which means every hacker, scammer, and social engineer on the planet now has this data.
What To Do Right Now
Don't wait. Do these five things today:
1. Change your Binance password immediately
Use a unique password you've never used anywhere else
Use a password manager (Bitwarden, 1Password, not your browser)
Make it long (20+ characters)
2. Upgrade your 2FA to hardware keys
Buy a Yubikey or similar USB security key
Binance allows 3x 2FA for withdrawals: USB key + mobile app + email
Turn off SMS 2FA completely if possible
3. Whitelist your withdrawal addresses
Only allow withdrawals to pre-approved wallet addresses
This prevents attackers from draining your account even if they get in
Yes, it's inconvenient. Your funds disappearing is more inconvenient.
4. Turn off 2FA cloud backup in Google Authenticator
If your Google account gets compromised, attackers get all your 2FA seeds
Use Authy with a strong master password instead, or write seeds on paper
5. Check if your email is in the leak
If you're in it, assume every password you've ever used is compromised
Change everything
One more thing: If you're using the same password for your email and your exchange, you're done. Attackers will reset your exchange password via email, then drain your account. Change your email password first.
Stat of the Week
$3.4 Billion Stolen in Crypto During 2025
Attacker | Amount Stolen | % of Total |
|---|---|---|
North Korean hackers | $2.02B | 59% |
All others | $1.38B | 41% |
North Korea's crypto theft jumped 51% year-over-year. Their all-time total: $6.75 billion.
And with over $130 billion now locked in DeFi smart contracts, the target keeps growing.
Source: Chainalysis, January 2026

The DeFi Crime Blotter
Former NYC Mayor Eric Adams accused of rug pulling his own memecoin
You can't make this up.
Eric Adams - former "Bitcoin Mayor" of New York City - launched a memecoin called "NYC Token" on January 13th. He held a press conference in Times Square. Said it would fight "antisemitism and anti-Americanism."
30 minutes later, the token crashed 80%. From $540M market cap to $87M.
On-chain data showed approximately $2.5M in USDC liquidity was withdrawn near the peak. About $900K was never returned. Crypto analytics firm Bubblemaps called it "such an obvious rug."
Adams denies profiting. His team claims the "market maker made adjustments." Sure.
The lesson? Even public figures with press conferences and stated missions can rug you. Actually, especially public figures with press conferences and stated missions.
SwapNet loses $16.8M to arbitrary call exploit
On January 25-26, attackers drained $16.8M from @0xswapnet on Base chain by exploiting an arbitrary call function in their smart contract.
The attack: Swapped 10.5M USDC for 3,655 ETH. Users who had granted one-time authorization to the SwapNet contract were at risk.
The team has disabled the contracts and is investigating. If you used SwapNet, revoke all approvals immediately.
Discord verification scam drains $14K
A user lost $14K (mostly USDC) by connecting their wallet to what they thought was a Collabland verification bot.
The trick: Fake Discord servers with 30-60 members. The user signed what looked like a "harmless" signature request. Funds drained instantly.
The vulnerability? "Vanity link sniping" - scammers grab expired Discord invite links and recreate fake servers with identical names.
Never join a Discord server with fewer than 100 members. Ever.
Solana drainer epidemic identified by ZachXBT
Pattern: New wallet → Bot interaction → Entire balance drained.
The attack vector: QR code phishing on fake websites that are pixel-perfect copies of official Solana dApps. One victim lost 210,000 $Penguin tokens in seconds.
The scary part? These scripts are looking at all your DeFi positions across multiple platforms. They know exactly what you hold.

The Bottom Line
The 149 million credential leak isn't a one-time event. It's a permanent expansion of the data available to attackers.
If your email is in that database (check now at haveibeenpwned.com), assume every password you've used in the past 5 years is compromised.
Here's what actually works:
Hardware 2FA keys (not SMS)
Unique passwords for every account (password manager required)
Withdrawal address whitelisting
Zero cloud backups for 2FA seeds
The attackers aren't getting dumber. They're getting better tools.
Don't be the person who loses six figures because you reused the same password from 2019.
Want to check a protocol before you ape? @serisitsafebot on Telegram gives you a risk score in under 5 seconds. Free. No signup. Just ask.
Don't get got.
Anson
P.S. Know someone still using the same password everywhere? Forward this to them.
Sources: TechRadar, ExpressVPN, Chainalysis, Bloomberg, @CertiKAlert, @zachxbt